Free Focus on Security Event October 5, 2018
Keynote: 8:30 AM
Name: Keith Rayle, Strategist, Fortinet, Inc.
Title: “The Role of Artificial intelligence and Machine Learning in Cybersecurity”
 |
 |
Location: Zlock Performing Arts Center
What is "AI-machine based learning” and how does Fortinet use this today to add security
Where is AI in the Fortinet story and how it relates to protecting your current and future.
Award Presentation 9:20 – 9:30
Presentation of the Certificate of Information Assurance Award
 |
For a student to be awarded the Certificate of Information Assurance the student must complete five courses and pass the five industry recognized certifications. The five courses are Fundamentals of System Security (ISC2 SCCP Certification), Introduction to Computer Forensics (AccessData ACE certification), Incident Response and Computer Forensics (CERT-Certified Computer Security Incident Handler), Ethical Hacking (CEH certification) & Network Monitoring, Security & Forensics (WCNA-Wireshark Certified Network Analyst). |  |
Breakout Sessions 9:40 – 10:30
Name: Ronald Bishof, Computer Information Sciences Instructor, Gwynedd Mercy University

Title: Surface, Deep and Dark Web
The Internet and Google are not synonymous. Google is a search engine that utilizes programs called web crawlers to collect information from hyperlinked pages. The data collected is indexed for retrieval and returned when a user does a Google search. However, the web pages returned by Google only skims the surface of the Internet. In fact, Google and other search engines only index roughly 10% of the Internet. This presentation will look at where the rest of the Internet is, how to get there, and what lies deep beneath the surface.
***
Name: Joe Walsh, MA. Instructor; Director, Master of Arts in Criminal Justice (MCJ)
Title: Cybersecurity Top 10
The number of cybersecurity incidents continues to grow rapidly. Organizations often struggle with decisions about where to focus their security resources. This presentation will review ten of the most critical areas that organizations can focus on in order to improve security and prevent incidents.
***
Name: Cerena Coughlin, (PH) (FBI)
Title: FBI Employment
What did you dream of doing when you grew up? Was it exploring space as an astronaut? Becoming a sports star and playing first base or defensive tackle for cheering crowds? How about suiting up in an FBI raid jacket and breaking down the door to get the bad guy? Well, there is the possibility that one of those dreams can be made a reality. Federal Bureau of Investigation Special Agent and Recruiter for the Philadelphia Field Office Cerena Coughlin will provide our audience a different perspective on the FBI, what it does, and who comprises its ranks. Coughlin will discuss the critical need for diversity in hiring, address the misconceptions people have about joining the FBI, and provide clear guidance for becoming a viable candidate. SA Coughlin is also the FBI’s Coordinator for the Philadelphia Chapter of InfraGard, the organization’s primary public/private outreach program to facilitate the sharing of information essential to ensuring the integrity of critical infrastructure. Please join us for this unique look at the FBI, its people, and the Bureau’s outreach efforts.
***
Name: Michael Cavanaugh, RPLU, CEH, Vice President, Director of Production Apogee Insurance Group, a Berkshire Hathaway Company
Title: Should I invest in Cyber Liability Insurance
What is it? What does it cover? Why do I need it? Cyber Risk is not a problem to be solved it is only a risk that can be managed. Not all Cyber Liability policies are created equal when it comes to coverage or risk management. The new generation of Cyber Liability insurance policies seek to help you manage that risk and be there when the inevitable happens. There are two types of companies: Those that have been hacked, and those that will be.
***
Name: Dale Yeager, CEO, THE PROBLEM SOLVING COMPANY

Title: School Safety
School safety current problems, trends and solutions will provide participants with current information on school based crime. Participants will learn: How technology increases school based crime, Up-to-date understanding of social issues affecting school safety & new tactics for predicting student aggression and violence.
Breakout Sessions 10:40 – 11:30
Name: Bob McCouch, CCIE · Principal Technologist, High Availability Inc.
Title: IOT Introduction
- Challenges in securing the Internet of Things the weak link
- Child predators targeting IoT devices in toys
- The evolution of consumer IoT and its vulnerabilities
***
Name: Dan Lezoche, Supervisor of Technology Services, Bucks County Intermediate Unit
Title: Your Password Sucks
This presentation will cover challenges regarding password security and how to avoid common mistakes. Multi-factor and password management options will be covered for both personal and organizational usage.
***
Name: Bret Pleines, InfoBlox

Title: Securing DNS
John will be presenting the number of ways in which the DNS protocol can be exploited to cause interruptions to service and ultimately be used to funnel data out of ones environment by breaking data files into DNS Queries and sending that data out through port 53.
***
Name: Rhonda Okamoto, Legal/ID Shield
Title: Your Blockchain Made Simple
Our decentralized networks open up endless opportunities to conduct global e-commerce with trusted Blockchain technology. Rhonda is the Ambassador for Sharenode, which is building a sharing community that helps companies grow and grows the community. We help educate business owners on how to increase loyal customers and built their fan base using our "Blockchain Blockbox".
***
Name: Pam King, Chestnut Hill College, Computer Science and Information Technology Department Instructor for Digital Forensics Program
Title: Clues in the Hard Drive
This presentation will discuss some of the specific digital forensic artifacts that forensic examiners can recover from computers hard drives or other storage devices, what they may mean, and how they can help in a criminal or civil investigation. Some items may be unknown or overlooked. These items are things forensic examiners can add to their "toolbox."
Breakout Sessions 11:40 – 12:30
Name: Thomas Heverin, Ph.D., Drexel University College of Computing & Informatics
Title: The Ease of Conducting Reconnaissance on Industrial Control System Devices
Location: Classroom 1
Industrial control systems (ICSs) include electric grids, nuclear power plants, ships, manufacturing plants, building automation systems and more. ICSs have increasingly faced significant threats such as the NotPetya ransomware attack that targeted energy companies, the power grid, airports, and shipping companies in 2017. Devices associated with ICSs can be easily discovered on the Internet via sites including Shodan, a search engine for Internet-connected devices. Additionally, in-depth reconnaissance and even exploits can be run on discovered devices all through open-source tools. This presentation will show how easy it is to conduct reconnaissance on ICS devices setting the stage for cyber attacks. By learning how adversaries can start their cyber attacks on discovered devices, cyber defenders can better protect ICSs.
***
Name: Joe Walsh, MA. Instructor; Director, Master of Arts in Criminal Justice (MCJ)
Title: Your Secret is Not Safe - Private Browsing
Most modern web browsers offer private browsing modes, but how private are they? This presentation will review the privacy offered by these features. Suggestions for forensic examiners will also be provided.
***
Name: Jamie Ellis, Cisco Cybersecurity
Title: Hyperconverged and the Cisco solution
Location: Classroom 3
In this session, learn about the latest security, privacy, and compliance features of Microsoft Azure. You’ll learn Storage and virtualization are changing. Exchange is moving to Office 365. Your employees are storing files on Google Docs. Meanwhile, your renewal contracts are expensive, the barrier to flash storage is expensive, and the egress charge on anything you put in the cloud is expensive. As traditional storage needs evaporate into the cloud and servers become more commoditized, you no longer need complex SANs and traditional converged architectures.
Join Cisco to learn how schools are adopting hyperconvergence to address the challenge of “doing more with less.” We will discuss how Cisco HyperFlex allows you to consolidate hardware footprints, maintenance contracts and hypervisor licenses, all while drastically simplifying your environment and improving performance.
***
Name: Chris Stafford, Stafford Consulting, Adjunct Instructor, Bucks County Community College
Title: End User Training
This session will focus on training your end users in safe email practices, safe internet browsing practices, and recognizing social engineering.
***
Name: John Sayer, ASK TECHNOLOGIES, INC.
Title: Integrating Wireless and Wired Network Security using WPA2/802.1X
Location: Classroom 5
Lunch 12:30 – 1:30
Name: Franco Cappa, CISSP, Cyber Security Advisor, Office of Cybersecurity & Communications, U.S. Department of Homeland Security
Title: Homeland Security Perspectives for Building Cyber Security Capacity, Capability
Breakout Sessions 1:40 – 2:30
Name: Scott Lynch, Manager, Security Operations Swedish Space Corporation, Adjunct Instructor, Bucks County Community College, CCNP Security, GCIH, GNFA
Title: Blue Team, Detect and Defend
Building up your defenses doesn’t have to be hard or cost tons of money. Learn what you can do today to start to defend your network using what you have today and what you can augment to give you visibility, defensibility and accountability.
***
Name: Cindy Casey, Computer Information Sciences Instructor, Program Coordinator, Gwynedd Mercy University
Title: Logic Bombs - Blown to Bits
A Logic bomb is a hidden program capable of delivering a malicious payload when triggered by some event such as turning on a computer or opening a file. Logic bombs can be used in a wide range of attacks from harmless pranks to cyberwarfare. While some logic bombs can be extremely complex, others can be written with only ten lines of code. Logic bombs are difficult to detect and diffuse because the malicious code is injected into, or are delivered by means of, some trusted service or applications. This presentation will discuss how easily logic bombs can be written or obtained, and how catastrophic they can be when activated.
***
Name: Kristy Patullo, Cisco Cybersecurity
Title: Endpoint Security
Discover the Threats You’ve Been Missing with Advanced Endpoint Protection
Traditional Anti-Virus solutions are no longer effective tools for endpoint protection. Today’s sophisticated attackers have learned to bypass these types of controls, leaving IT staff with continuous efforts to clean or re-image compromised endpoints or servers. In addition, even the best security tools are not 100% effective. When a compromise does occur, it is generally detected far too late to mitigate the damage, and it is difficult to know how widespread it is. So IT administrators are often stuck playing a game of whack-a-mole after an attack.
***
Name: Anthony Saracino, IT Security Officer, Bucks County Community College
Title: Rethinking Defense in Depth
The focus of IT Security has always been to manage and control risk to an organizations critical assets. One way to protect an organizations information assets is through a defense in depth model in which multiple defensive mechanisms are deployed. This layered approach increases an organizations overall posture while also addressing different attack vectors. This presentation will discuss the traditional defense in depth model to control IT risk while also diving into other models. The other models that will be presented are the Cyber Kill Chain Methodology, the Mitre ATT&CK ™ Framework, and Zero Trust Architecture.
***
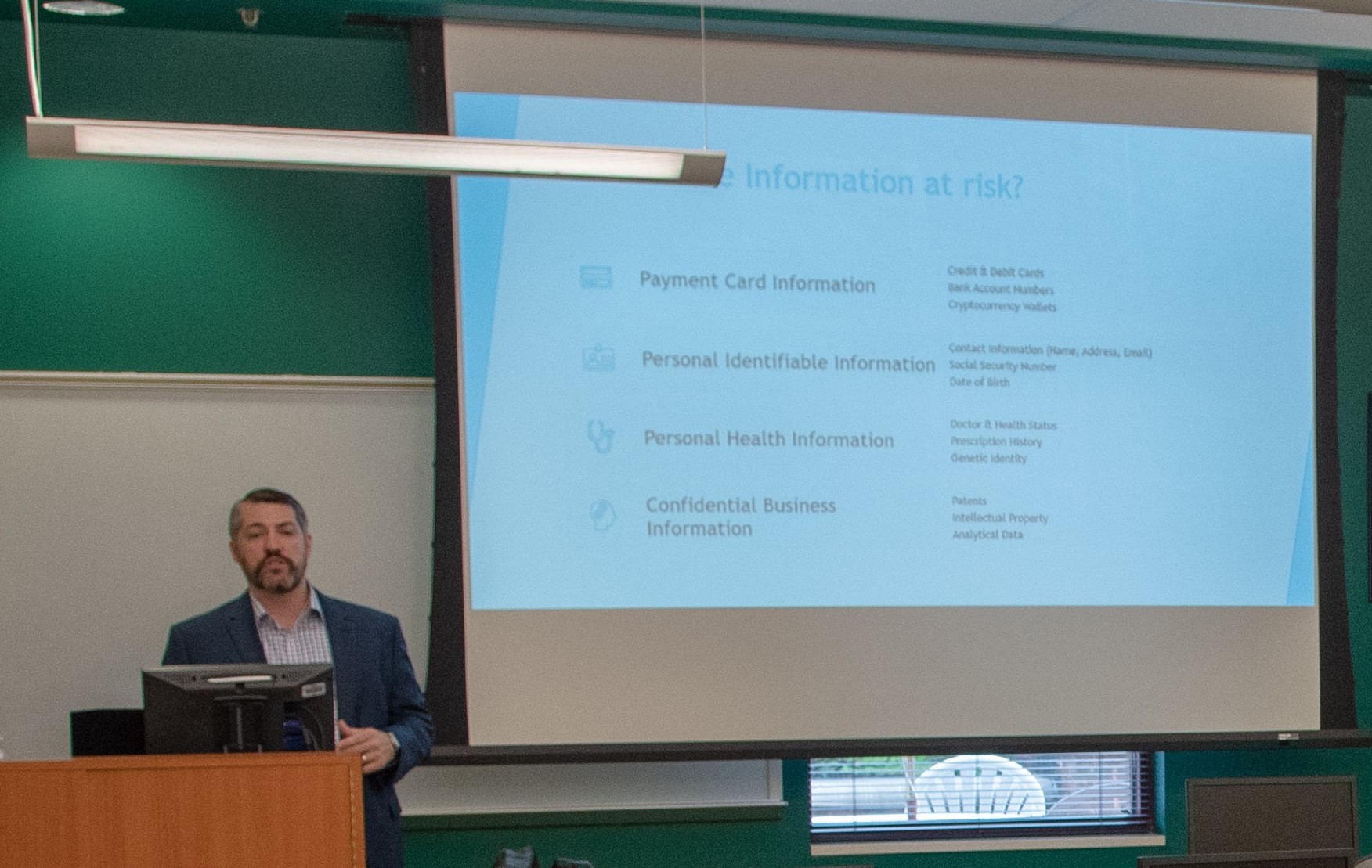
Name: Ken Brown, VP, Corporate IT & CISO, Frontline Education
Title: Security in Cloud: How do things Change?
Securing your public cloud assets has its challenges and advantages over on-prem infrastructure. Although many datacenters have been undergoing virtualization, the cloud brings with it even more abstraction and can require a mind-shift in the way a security practitioner operates. We will get into the “shared responsibility model” for Amazon AWS and discuss what changes and what stays the same. We will spend time on some of the core security architecture components such as IAM, VPCs, WAF, Shield and others. We will also look at common security pitfalls when moving workloads to the cloud.
***
Breakout Sessions 2:40 – 3:30
Name: George Frazier, M.Ed., CISSP, GSNA, GCIH, Director of Information Systems, Lower Merion School District
Title: Red Team Your Network
This presentation will introduce Red Teaming and provide participants with several Command and Control scenarios and that can be used to sharpen incident response team skills and improve network security. Miscreants and criminals want to gain a foothold on networks and use the available resources for their gain. Would you know if there was a compromised system on your network being controlled through a command and control channel? What logs would you review in order to find suspected command and control activity? This session will give participants a starting point to exercise defenders and reduce the vulnerabilities used to maintain persistence in a network.
***
Name: Cindy Casey Computer Information Sciences Instructor, Program Coordinator Gwynedd Mercy University
Title: Steganography & the Xbox: How Terrorists may be Hiding in Plain Sight
Video game consoles have traditionally been viewed as home entertainment devices. However, today’s gaming systems are sophisticated communication hubs with networking capabilities equal to those found in modern computers. Not only do they provide users with the ability to communicate via email, video, audio and text chat, but it enables them to connect to their systems from a PC or smartphone, transfer pictures, videos, and files, and surf the Internet or dark web. Some of these communication capabilities have been exploited by individuals to plan and commit a variety of criminal and terrorist activities. This presentation will explore how terrorists are using gaming consoles to convey secret messages, spread propaganda, share files, and recruit members.
***
Name: Mike Shellenberger, Client Warrior,

Title: Defending against Business Email Compromise (BEC)
We are seeing a tremendous uptick in Business Email Compromise (BEC) attacks within the past year. Credential phishing and spear-phishing are two of the most successful email attack methods we’re seeing as most email security platforms do not effectively stop these style messages. Join us for an informative session on how email authentication protocols such as DMARC, DKIM and SPF in conjunction with industry-leading solutions from Proofpoint can protect your organization.
***
Name: Ken Pyle, CISSP, HCISPP, ECSAv8, CEHv8, OSCP, OSWP, EnCE, Sec+ DFDR Consulting LLC, Digital Forensics, Incident Response, Cyber Security
Title: OSINT/Social Engineering - Weaponizing Psychology and Sociology and Interrogation Strategies for better phishing
Location: Classroom 4
Identifying Social Engineering threats to an organization is a critical function of security. With SE being the #1 vector of attack for threats, managing risk and exposures through advanced analysis and threat modeling is critical. This session will outline advanced tactics, psychological profiling methods, tradecraft and open source investigation methods not previously explored which can be used to both attack and defend a company.
Attendees will understand new methods and attacks penetration testers as well as defenders can apply to better secure their users.
***
Name: Cody L. Hofstetter, Founder & CEO Sovereign Cyber Industries
Title: Social Engineering: A Pentesters Guide to People
Social engineering used in the context of information security refers to the psychological manipulation of people into performing actions or divulging information. For this presentation, we'll delve into the methods and tactics of penetration testers and how you can apply them to enhance your everyday life. From calling on the phone to in-person interactions, you'll learn to view the way you communicate from a completely different perspective.